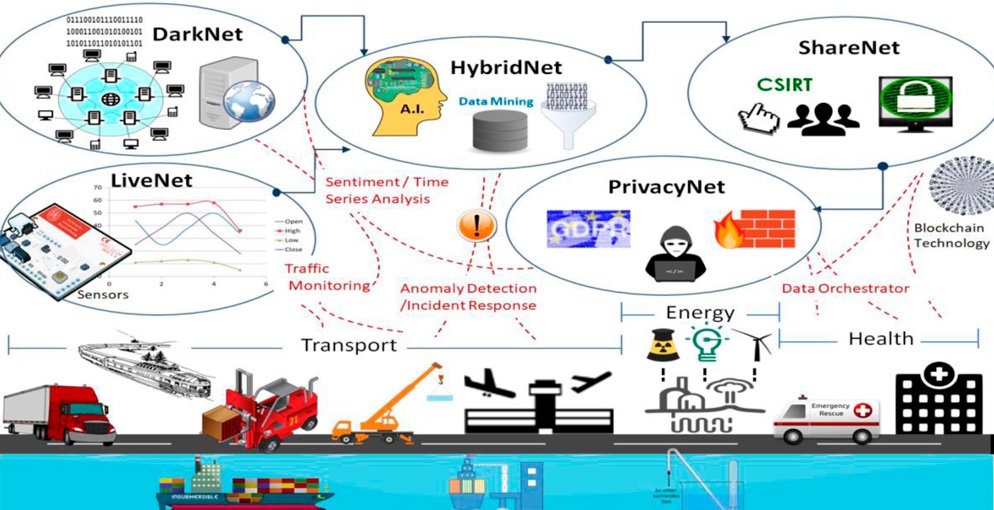
The architecture of the cybersecurity knowledge base. DDoS: distributed... | Download Scientific Diagram

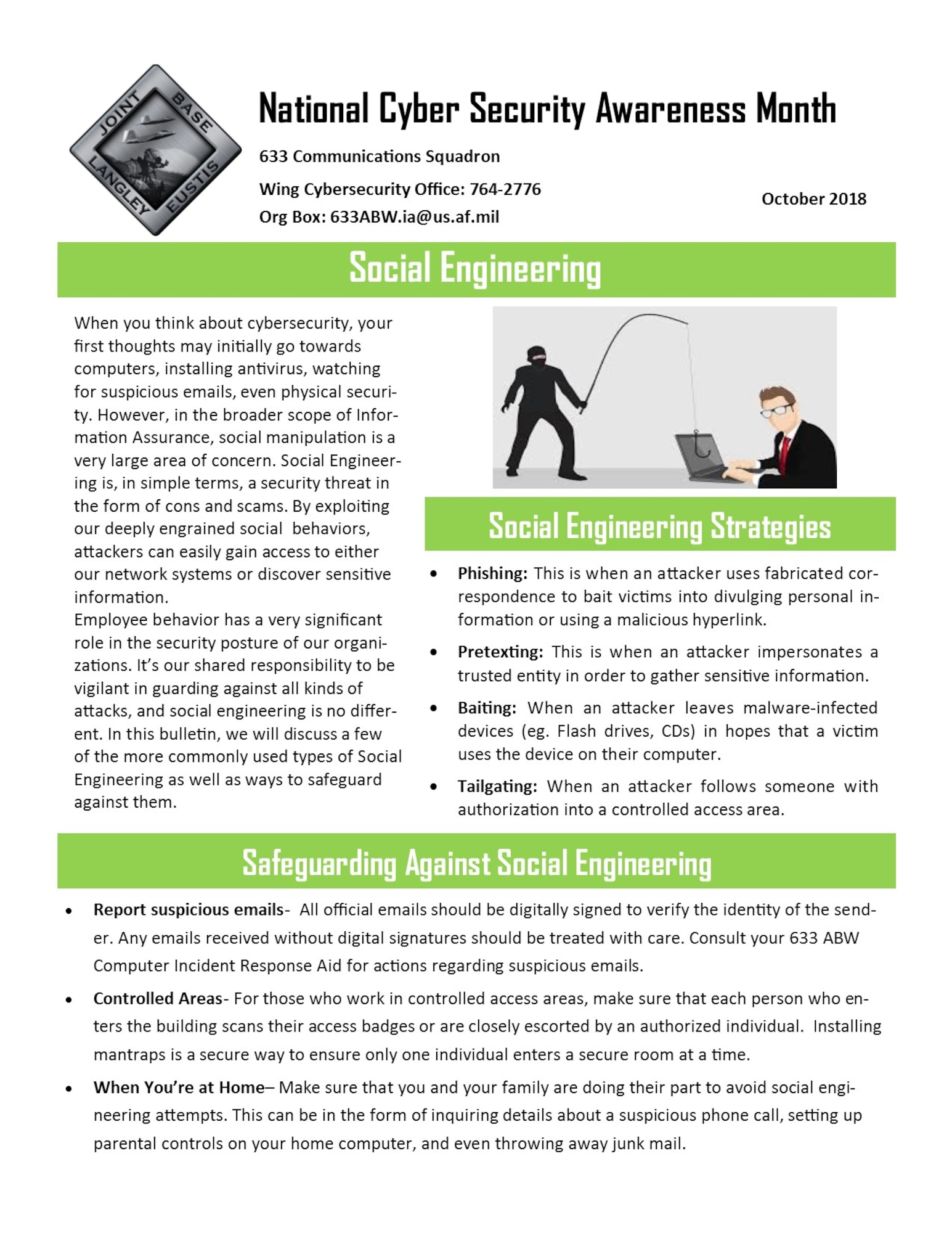
Building a base of cybersecurity experts in Indiana - WISH-TV | Indianapolis News | Indiana Weather | Indiana Traffic

Inside the British military base where young hackers learn to stop cybercrime | UK security and counter-terrorism | The Guardian
Cyber Security System Technology Icons Set Vector. Cyber Security Software And Application, Padlock And Password For Data Base And Information Protection From Virus Line. Color Illustrations Stock Vector | Adobe Stock